penetration test:
Infiltration testing is an authorized and programmed process to exploit vulnerabilities to infiltrate server, network, or application resources. In fact, intrusion testing is a method of assessing the security of a computer system or network by simulating an attack by a hacker or malicious intruder. The intrusion testing process is an active analysis of the system to find any holes, vulnerabilities and technical defects that are potentially a security vulnerability of the system. This analysis is performed as a potential hacker and can use active security vulnerabilities to carry out attacks. All security issues should be presented to the system owner along with an assessment of their importance as well as suggestions for mitigating the effects of risks or technical solutions. Penetration testing can be conducted using internal sources such as the host security system or external sources such as internet connection. In this test, a series of automatic or manual tools are usually used to test the system resources.
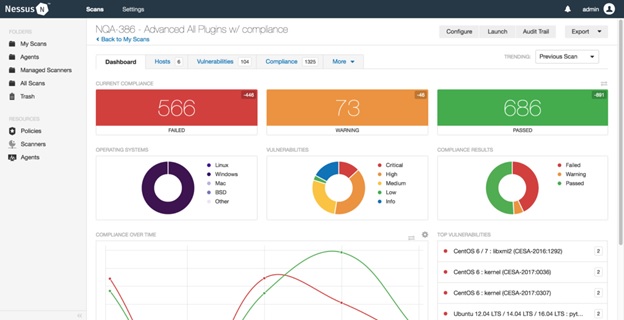
Nessus
Nessus software is used to detect vulnerabilities at the network level. This software is able to perform permeability tests based on both white box and black box tests. Nessus software supports a variety of different structures for scanning. These structures include various operating systems, types of virtualizers, and network protocols. The core of Nessus is its plugins. In fact, each of the plugins represents a vulnerability that Nessus has categorized.